|
|||||||||||
|
|
|
|||
|
By Mike Mitchell |
||||
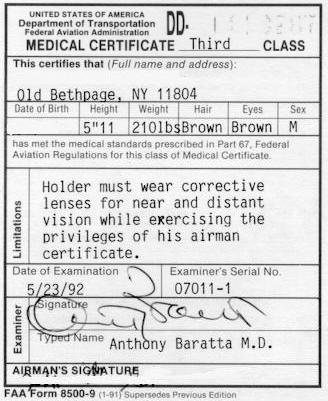 |
June 24, 2010 - An audit was conducted on the Federal Aviation Administration (FAA) by the Department of Transportation (DOT) at the request of the Chairmen of the House Committee on Transportation and Infrastructure and its Subcommittee on Aviation. The audit was to determine if pilots personally identifiable information (PII) is properly secured from unauthorized use or access, and assess FAA’s progress in establishing mechanisms to identify airmen holding current medical certificates while receiving disability pay (see Southwest Pilot Pleads Guilty To Fraud). The FAA requires airmen (pilots) to hold a medical certification of their medical and mental fitness to operate aircraft. Under DOT, the Office of Inspector General (OIG) conducted their work by interviewing officials from the FAA’s Civil Aerospace Medical Institute located in Oklahoma City, Oklahoma, the FAA’s Headquarters in Washington, D.C. as well as representatives from the FAA’s contractor and Aviation Medical Examiners' (AME) private medical support staff at various locations. OIG also spoke with officials from FAA's Office of Budget Policy Division. The MSS currently stores more than 18 million medical records supporting the medical assessment of over three (3) million airmen. |
|||
|
|
||||
|
|
||||
|
There are serious
security lapses in FAA’s management of In addition, the FAA has not ensured secure configuration of MSS computers in accordance with the Department’s baseline standards to reduce the risk of unauthorized access and corruption. Specifically, OIG found vulnerabilities on MSS computers, such as configuration allowing intruders to install malicious codes on FAA user computers. Inadequate contingency planning also threatens the service continuity of MSS. Combined, these weaknesses make airmen’s PII vulnerable to unauthorized access and use and potential falsification of medical certificates that could lead to unfit airmen being medically certified to fly. During the course of OIG review, the FAA took immediate action to enhance security protection by working with doctors to remove thousands of separated medical staff's access to MSS and retracting millions of PII records from the contractor’s site. However, additional improvements are needed to adequately secure PII data from unauthorized use.
The FAA has made
limited progress in identifying airmen who receive disability benefits
while holding medical certificates. While FAA has a draft matching
agreement with the Social Security Administration (SSA) to reconcile
data in MSS and SSA’s disability benefits system, it has yet to
establish a target date for completing the interface. Further, FAA has
yet to coordinate with other benefits providers, such as the Department
of Veterans Affairs and the Department of Labor.
FAA continues to rely on airmen to disclose potentially disqualifying conditions when applying for medical certificates. FAA recently announced a onetime, limited opportunity for airmen to reveal previously undisclosed depression and use of antidepressant medications without being subject to FAA enforcement action (see Pilots Who Suffer From Depression Maybe Able To Fly Under FAA Proposal). This step, however, does not take the place of a comprehensive approach to undisclosed medical conditions. Accordingly, the FAA needs to expedite computer matching agreements with disability benefits providers, implement the checks under those agreements, and take appropriate enforcement action where falsifications are found. OIG Recommendations OIG recommend that FAA's Associate Administrator for Aviation Safety, in consultation with the FAA Chief Information Officer, implement the following actions to improve the security, reliability, and accuracy of sensitive airmen medical information and tighten controls to ensure that unqualified airmen do not receive a medical certification enabling them to fly. Secure Sensitive Airman Records: 1. Finalize implementation of MSS application security administration improvements to ensure only authorized medical staff has access to MSS, as identified by the FAA’s Federal Air Surgeon in June 26, 2009, internal memorandum and report progress to the FAA Administrator. 2. Implement restrictions on AME access to inactive airman records based on a need to know.
3. Develop
documentation detailing the intended controls regarding how users
function within their assigned security roles, how the MSS application
enforces both access control and segregation of duties, and the features
of the application to assist security administration. Deter and Detect Unauthorized Access and Invalid Airman Data: 4. Encrypt sensitive airmen PII stored in MSS as well as MSS user passwords, and develop agreements as appropriate to ensure airmen PII provided to other systems is also encrypted.
5. Implement
multifactor user authentication, as required by OMB, and the
Department’s Secure Remote Access capability for all MSS users with
remote access to sensitive PII.
6. Require and
validate that all 7. Implement the audit and accountability recommendations received during the previous certification and accreditation process to help identify inappropriate access to sensitive PII (abuse of access privileges) and ensure data extract/query has been erased within 90 days from its creation date. 8. Develop edit checks on the integrity of airman application data when entered into MSS. Configure MSS Systems to Reduce the Risk of Attack: 9. Mitigate the vulnerabilities identified by OIG on MSS computers that could allow unauthorized access and potentially jeopardize confidentiality, integrity, and availability of sensitive PII. 10. Configure MSS computer systems in compliance with applicable Government standards including ensuring vendor security updates are applied, the Web site locks the user account after three unsuccessful attempts, all passwords on the MSS database are in compliance with standards, and that the application will enforce a session lock after 15-minute inactivity for all users in accordance with OMB and DOT guidance.
11.Perform and
document security testing as a continual part of the MSS development
process to confirm that security features remain in effect and are still
functioning properly when system changes are made. Mitigate Contingency Planning Weaknesses that Threaten Service Continuity: 12. Acquire a back-up server, finalize the Memorandum of Understanding with the selected alternate processing site, and conduct a comprehensive contingency test at the alternate site in accordance with Government standards. 13. Upgrade the database system to a version supported by the software vendor. 14. Develop back-up database administration capability in the event the primary. Detect airmen receiving disability benefits:
15.Work with SSA
and other disability benefits providers to establish a target completion
date for performing computer matching to identify airmen applying for,
or holding, medical certificates and receiving disability benefits. |
|
|
| Other News Stories |
| ©AvStop
Online Magazine
Contact
Us
Return To News
|
|


